Digitisation wave is spreading at an exponential rate and is influencing almost every facet of human life. The convenience provided by digitisation has enabled us to use digital tools to seamlessly complete multiple tasks such as purchase of tickets and goods and executing financial transactions.
A seamless and secure e-ecosystem is the key requirement for fuelling further growth of digitisation. For achieving this, it is necessary to accurately identify each user and establish a unique ownership of the underlying transactions. The increased use of online platforms, including social media networks, for accessing financial services has led to an alarming growth in cybercrime. Instances of email1 accounts, professional network passwords2, and credit card details being compromised3 have become more frequent, and the task at hand is to restore the confidence of the consumer in the security of digital transactions.
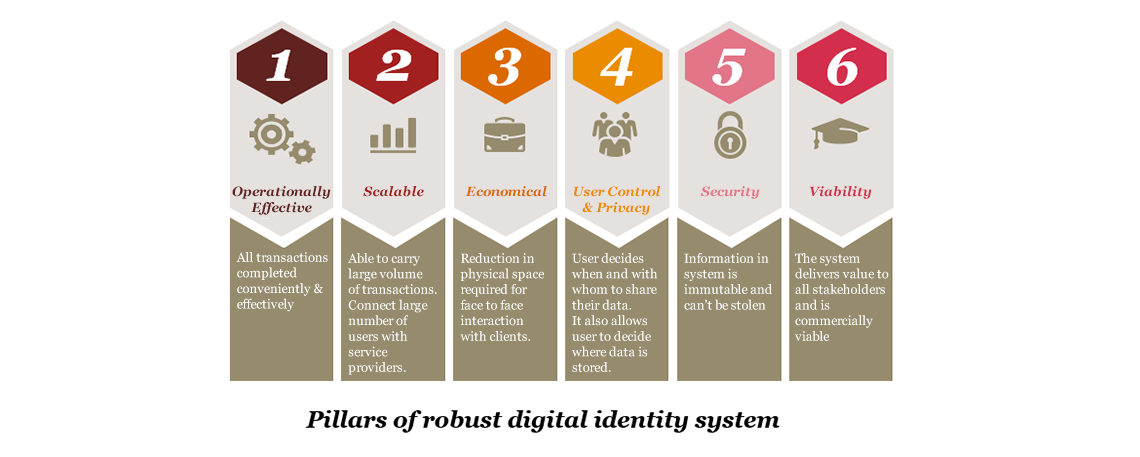
Traditional identity systems are cost ineffective, fragmented and inadequate in the face of sophisticated attacks, and they limit the ability of financial institutions to provide a seamless transaction experience. Thus, deploying robust and modern digital identity systems is the next step to establish the true digital identity of individuals, companies and assets.
The blockchain solution
A digital identity solution based on blockchain or distributed ledger technology (DLT) is economical, immutable, secure and easily accessible, while providing a legitimate audit trail. DLT is an incorruptible decentralised ledger that not only provides a transaction medium but also acts as a repository of all transactions in hashed digital packets called blocks. The advantage of a DLT-based identity system over traditional ones is its ability to record each identity shared in the global network and maintain continually reconciled data throughout the network.
How it works
The technology empowers consumers to restrict sharing of their identity with only trusted local or remote entities. DLT-based digital identity works on the public key cryptography principle, where every identity is a ‘key pair’ consisting of a public key used to send data to an address and a private key to read data4 . For example, a customer shares her digital identity/know your customer (KYC) documents with a DLT-enabled financial institution to authenticate herself and qualify her digital identity on the DLT platform. The institution can then share customers’ data with other entities for legitimate purposes, only after receiving the customer’s consent. This facility benefits all parties in saving time and money by eliminating the need for KYC at multiple places within or outside the country, thereby optimising costs involved in accurately establishing identities. With a single identity across the globe, it also aids regulators to monitor fraudulent activities, such as money laundering, more effectively.

The adoption
Organisations in many developed countries are excited about this new technology. They have realised that DLT is more resilient, economical and easily manageable in comparison to the current fiat currencies and are experimenting various use cases.
The technology has seen adoption in India as well. A few commercial banks and research institutions have taken the initiative to experiment DLT–based solutions for trade finance and cross-border remittance solutions5. However, it is necessary to expand the scope of digital identity solutions to ensure interoperability and standardisation in customer-facing processes, in-house operations and risk management practices to reap further benefits.
The way forward
Though institutions have been focusing on efficiency gains, in the long run they may replace the antiquated kludge of inefficient technology solutions. DLT will see further growth if the technology is put to use in an individual’s day-to-day activities, like retail purchases, transferring or archiving documents securely, and opening a bank account instantly with a single click.
DLT-based identity solutions have the potential to reduce risks considerably which will allow users to try new things, curate new business models and completely revolutionise the business ecosystem.
Sources:
1Goel, V. and Perlroth, N. (14 December 2016). Yahoo says 1 billion user accounts were hacked. The New York Times. Retrieved from https://www.nytimes.com/2016/12/14/technology/yahoo-hack.html (last accessed on 29 September 2017)
2Pagliery, J. (19 May 2016). Hackers selling 117 million LinkedIn passwords. CNN Tech. Retrieved from https://money.cnn.com/2016/05/19/technology/linkedin-hack (last accessed on 29 September 2017)
3Silver, J., Goldstein, M. and Perlroth, N. (2 October 2014). JPMorgan Chase hacking affects 76 million households. The New York Times. Retrieved from https://archive.nytimes.com/dealbook.nytimes.com/2014/10/02/jpmorgan-discovers-further-cyber-security-issues/ (last accessed on 29 September 2017)
4Higgins, C. (9 May 2017). Digital identity Part 1. Storing sovereign identities on the blockchain. Crypto Insider. Retrieved from https://cryptoinsider.com/digital-identity-part-storing-sovereign-identities-blockchain/ (last accessed on 29 November 2017)
5Das, S. (23 March 2017). An in-depth analysis of how blockchain is unfolding in India. CIO & Leader.












