
Need for data privacy
As data becomes crucial for enterprises and governments around the world, there has been a multifold increase in the volume of data being created, stored and processed, resulting in it becoming a critical commodity. India is gradually emerging as a data-driven economy. As per a report by the Telecom Regulatory Authority of India (TRAI),1 as of June 2019, out of 665.31 million internet subscribers in India, 21.67 million were wired internet subscribers and 643.64 were wireless internet subscribers. These numbers indicate that personal data is becoming available in the public domain due to high mobile internet usage. Statistics show that 30.5% of Indians are below the age of 252 and extensively use mobile apps to access social media. Therefore, it becomes imperative for the government to protect personal data of its citizens.
Different countries have enacted data protection laws and regulations, such as the General Data Protection Regulation (GDPR) for citizens of the European Union (EU) and the California Consumer Privacy Act (CCPA) for residents of California.
The Personal Data Protection (PDP) Bill, 2018,3 is slated to become India’s first proper Legislation on data protection. The draft of the bill is based on recommendations on data protection and privacy by a government-constituted panel.
In this article we will not be explaining the Indian data privacy law but identifying areas of the law, which data governance and technology can help to comply.
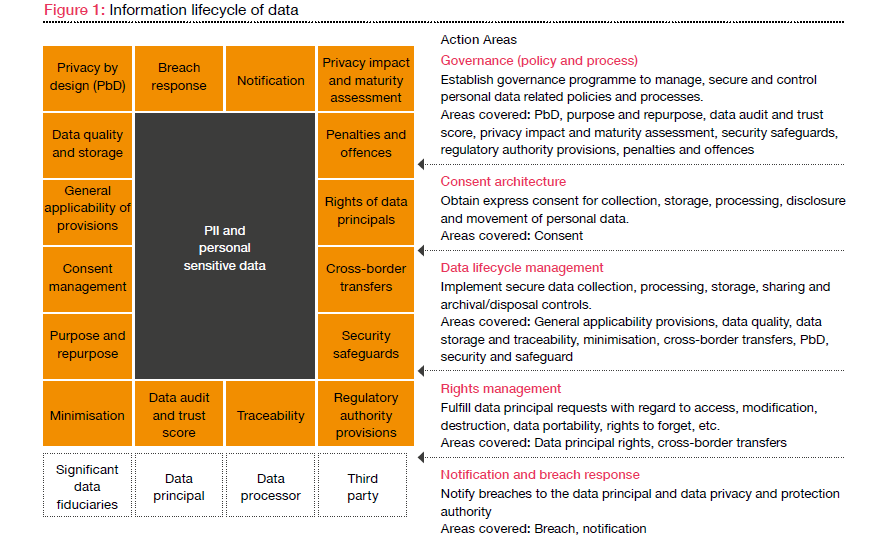
The PDP Bill touches upon various aspects of information lifecycle, as shown in Figure 1. The draft bill states that the government will have jurisdiction over the processing of personal data, if such data has been used, shared, disclosed, collected or processed in India. The government will also have jurisdiction over the personal data collected and processed by the companies incorporated under Indian law, irrespective of the place of origin of the data.
The five action areas defined in Figure 1, when implemented, would help an organisation be compliant with data privacy laws. In the subsequent sections, we will further explore these action areas.
Role of data governance in data privacy
Data governance and data privacy go hand-in-hand. Although data governance doesn’t solve all data privacy requirements, it helps cover a lot of ground for compliance with privacy regulations. A good governance operating model helps to ensure that compliance is put in place across the organisation suitably. Data governance office (DGO) is now a major requirement for various data privacy compliances such as GDPR in the EU and a similar office will also become a primary requirement for India’s data privacy laws. A comprehensive data governance policy sets appropriate data monitoring processes and metrics in place to ensure smooth functioning of business, while meeting data compliance requirements.
Data privacy laws mandate that organisations know and record where their data resides, who uses the data, how the data is used and how the organisation’s business process is related to the data. An effective way for organisations to ensure compliance with such regulations is to build a comprehensive data inventory and data map that identifies the necessary criteria of compliance. Data owners and data stewards can record such information as business and technical metadata, tagging and mapping it with business processes to facilitate transparent data lineage and data mapping.
Data classification is another method used for data governance and to protect data privacy and meet regulatory requirements. With the help of data classification, organisations can adopt proactive measures to ensure compliance with regulatory requirements. Data can be classified and categorised based on data access frequency, user activity, volumes, etc. This can enable risk-based prioritisation of any data privacy-related issues and identify gaps in the current data.
The data access component of data governance can help address data security risks. Drafting clear and definite access guidelines for both internal and external exchange of data can help control data flow and ensure that only authorised parties have access to the data. It is also necessary to evaluate and continuously monitor all the security risks to have a greater control on information. Data-to-process and data-to-role relationship matrices are some of the ways to manage data access.
Role of technology in data privacy implementation
Various technological solutions can be used to achieve the goal of data privacy and compliance in an organisation. These technologies cater to regulatory needs related to data privacy and protection and ease the functioning of organisations. Some of the scenarios where technological solutions can help the organisation comply with various regulatory requirements are discussed below.
Tools and technologies which can assist in ensuring data privacy and managing data efficiently in its lifecycle journey are:
- database management systems
- business intelligence tools
- application frameworks
- identity management technologies
- change control systems
- access and authentication systems
- workflow management solutions
- usage management solutions
- data discovery and cataloguing solutions
- security solutions
- data lineage tools.
Data privacy enablers
For organisations to wholly comply with data privacy laws, restructuring is often required. For example, systems and technological solutions in an organisation should be designed in such a way that they ensure: (i) data processing is limited to the purpose for which the data was collected; and, (ii) access to personal data is granted only to those who need it. Also, an automated consent management framework would help in easy and error-free management of requests related to PII data.
For organisations to comply with strict privacy standards and have greater control over data, there is a need to adopt the principle of PbD, along with privacy by default. Privacy by default is a product-related approach which requires controls to be put in place across all the data collection points. It implies that once a product or service has been released to the public, the most stringent privacy settings are applied by default, with no manual intervention from the end user. PbD requires the organisation to make robust privacy policies which reflect in both technical and business conduct. PbD can be achieved by:
- implementing a privacy impact assessment for each system across the organisation.
- having a standard risk assessment procedure in place to deal with breaches and issues.
- reviewing and updating data life cycle management techniques.
An automated consent management framework is an enabler which addresses the challenge of customer trust with respect to their personal data and information and adds to customer delight. This framework is a customer touchpoint and is used to raise, validate and process requests raised by customers. Given that post-implementation of the data privacy law in India, an organisation would need to process multiple requests to update and delete PII data, an automated solution based on a welldefined framework would provide a quick, secure and accurate turnaround time for such requests.
Conclusion
In order to comply with data privacy laws, organisations would need to change their policies and practices on data management. A sound data governance framework and technological solutions are the two major drivers in an organisation’s journey towards compliance. Organisations must have in place policies to ensure checks and balances for every data transition which takes place during the information journey. Organisations would also require solutions to identify PII data across application landscapes and execute appropriate action, based on client requests and principals of data privacy laws. Automated consent management to manage multiple PII data-related requests is the need of the hour. Technology solutions can also help organisations address concerns related to data security. A central communication channel, established with data principals, can certainly go a long way towards ensuring clients’ trust and compliance with data privacy laws.
Acknowledgments: This knowledge series has been researched and authored by Abhishek Chaurasia, Aditi Tripathi and Samiksha Wahi.












