Tackling risk with AI/ML
Next-generation AI for fraud risk assessment
PwC’s 21st CEO Survey5 reported that 40% of CEOs across the world are extremely concerned about cyberthreats. From the back office to front-end application users, security needs to be embedded as the core strategy to build strong connected ecosystems, spanning boundaries and technology platforms. AI is fast emerging as the best option to handle the growing volume of transactions and consequently curb fraud arising from data and identity breaches, thereby protecting businesses against hefty losses.
From rule-based to intelligent safeguards
Traditionally, companies used fraud detection systems that based on expert-driven rules to make automated decisions. These companies followed the pre-defined ‘if X then do Y’ logic to flag suspicious users to the transaction processing engine and prevent them from completing transactions. However, with the ever-growing digital penetration leading to steep growth in the number of transactions taking place every day, it becomes impossible for experts to study every data point, identify patterns and come up with intuitive rules to flag outliers. Additionally, these rules can generate false positives or false negatives. Hence, the traditional methodology is not robust enough to handle data mining required to reveal risk predictive relationships. That is where ML engines come in; ML systems allow for more accurate rule creation and pattern building, developing insights purely from data.
Integrated views give greater insights
The use cases for ML are bound by the data available to such technologies to view and learn from. The next stage of utilising such technologies for more robust risk and fraud monitoring would be to integrate data across touchpoints and channels for stronger monitoring and more meaningful pattern recognition. Organisations should leverage the ability to consume and integrate data from different digital channels to create single views that could provide more insights than disparate monitoring. Coupling this with real-time alerts delivery to relevant internal stakeholders and utilising similar digital channels of communication which also allow users to respond with equal levels of urgency (e.g. chatbots) would especially improve company defences against fraud and cyberthreats and align organisation abilities to the real-time nature of such threats.
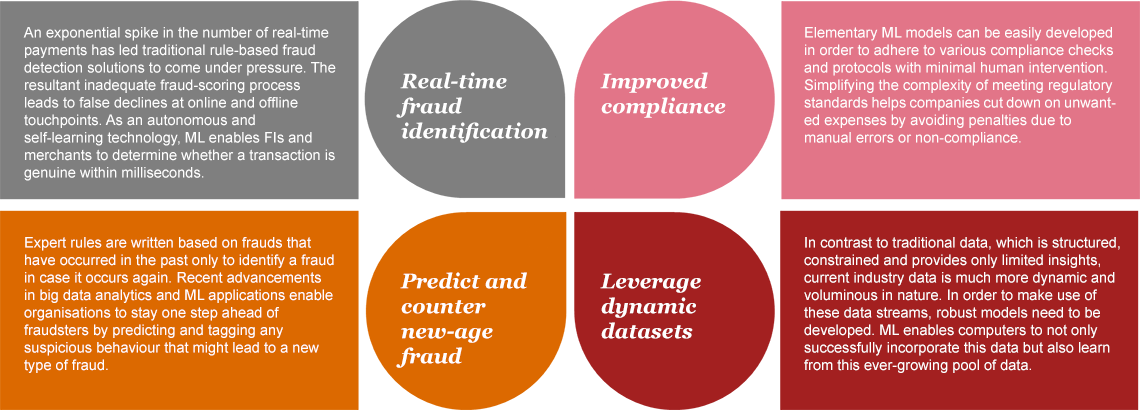
Benefits of leveraging AI to counter fraud
Using AI and ML to improve prevention and cure strategies
AI and ML technologies can significantly improve the efficacy of early warning signal models, providing organisations with better insights into which accounts are headed towards non-performing assets (NPA) status. Proactive strategies to focus on such high-probability cases would enable more efficient deployment of resources and reduce the inflow of NPAs. Leveraging alternative data to further enhance such early warning signal models is one of the many strategies that FS players are already adopting in an effort to manage credit risk exposure.
Another area where AI and ML can play a significant role is resolution. The recent RBI guidelines on NPA resolution focus on the need for a ‘resolution plan’ for accounts in default. Lenders can use ML techniques to develop more meaningful and specific resolution plans that would have higher chances of success by learning from patterns in resolution based on strategies deployed, customer segments, product types and other factors. Collection efficiencies can also be streamlined by providing insights to collection channels on successful strategies.
Building a future-ready and secure ecosystem
Obtaining the right information from customers at the right time and in a fair manner would be the key for any company to be at an information advantage. By ensuring the delivery of contextual insights within the same time span, the company would be able to provide its customers with a differentiated experience. Such a capability would require multiple integrations with enterprise applications and other third-party applications. While a number of organisations have already acknowledged the advantage of such a set-up, there is a need to ensure that such real-time data access and storage is protected and safe.
A safe and secure technology ecosystem will be built on four key pillars:

Four key pillars of a safe and secure set-up
Sources:
5PwC. (2018). 21st CEO Survey. The anxious optimist in the corner office. Retrieved from https://www.pwc.com/gx/en/ceo-survey/2018/pwc-ceo-survey-report-2018.pdf (last accessed on 9 May 2018)
Contact us














